In the increasingly digitized landscape of financial services, managing credit security has become paramount. As consumers and enterprises alike grapple with rising threats such as identity theft, fraud, and data breaches, innovative tools are essential for safeguarding credit information. One such powerful resource is ExperianVerify, a sophisticated verification platform designed to enhance credit security, streamline identity validation, and foster consumer confidence. With its advanced capabilities rooted in industry-leading data practices, ExperianVerify has established itself as a cornerstone in modern credit management strategies. This article explores how to leverage ExperianVerify effectively, outlining best practices, practical applications, and how it integrates within broader credit security frameworks.
Understanding ExperianVerify: A Foundation for Secure Credit Verification
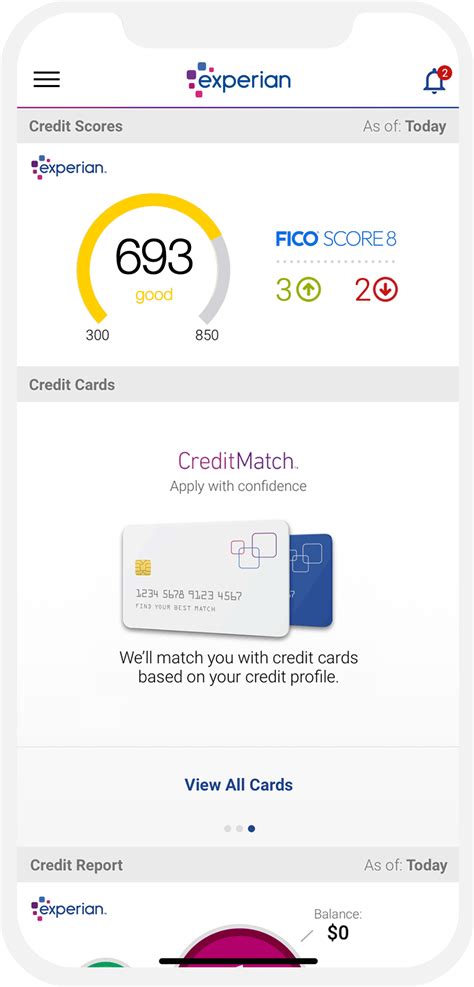
Before diving into strategies for use, it is vital to establish what ExperianVerify encompasses. Developed by Experian, one of the three major credit bureaus globally, this platform offers multifaceted services tailored for both lenders and consumers. Its core functionality revolves around authenticating identities, verifying applicant information, and preventing fraud — foundational elements in maintaining robust credit security. Unique to ExperianVerify is its utilization of real-time data analysis coupled with sophisticated algorithms, which together provide a comprehensive verification ecosystem. This system helps organizations mitigate risks associated with fraudulent applications, unauthorized credit access, and erroneous data entries.
Core Components and Features of ExperianVerify

To harness ExperianVerify effectively, understanding its principal features is paramount. These include:
- Identity Confirmation: Utilizing multi-factor authentication processes to verify the identity of applicants or account holders.
- Data Enrichment: Enhancing application information with additional data points to ensure completeness and accuracy.
- Fraud Detection: Identifying suspicious patterns via machine learning algorithms that flag irregularities or potential identity theft.
- Consent Management: Ensuring compliance with privacy laws by managing consumer consent workflows during verification processes.
- Integration Capabilities: Connecting seamlessly with existing credit bureaus, CRM systems, and loan origination platforms.
This suite of features, underpinned by Experian’s extensive data repositories, provides a robust foundation for institutions aiming to boost their credit security protocols. Each component contributes to an ecosystem where data integrity and risk mitigation go hand-in-hand.
Implementing ExperianVerify: Practical Steps for Maximum Impact
Effectively employing ExperianVerify requires strategic implementation across different stages of customer onboarding or credit assessment. Here’s an in-depth look at each step:
Step 1: System Integration and Customization
Initialization begins with integrating ExperianVerify into your existing workflows. This requires API configuration, aligning verification modules with your platform architecture, and customizing workflows to suit specific risk profiles. By tailoring the verification parameters—such as threshold levels for fraud alerts or identity confidence scores—you ensure the system aligns with your organization’s security posture.
Step 2: Establishing Verification Protocols
Once integrated, clear protocols must be established. For example, setting mandatory verification steps for high-value transactions or new application entries. In this context, organizations might assign different verification levels based on the applicant’s credit score, transaction size, or industry standards. The goal is to optimize fraud prevention without creating friction for legitimate users.
Step 3: Training and Staff Empowerment
Technology only achieves its full potential when backed by informed personnel. Training staff on how to interpret verification alerts, handle suspicious activity reports, and manually override automated decisions when appropriate is essential. This nurtures an environment where human judgment complements technological safeguards, enhancing overall security.
Step 4: Continuous Monitoring and Feedback
Operational effectiveness hinges on ongoing performance assessment. Utilizing dashboards and analytics tools provided by ExperianVerify enables proactive monitoring of verification metrics, such as false positive rates or detection accuracy. Regular feedback loops allow for calibration of verification parameters, ensuring that the system adapts to evolving fraud tactics or regulatory changes.
Maximizing Credit Security Through Best Practices
Beyond the core implementation, real mastery involves proactively leveraging ExperianVerify’s capabilities in broader security strategies. Some recommended best practices include:
- Enhanced Data Privacy Compliance: Ensuring your processes align with regulations such as GDPR or CCPA, especially regarding consumer consent and data handling.
- Multi-Layered Verification Approaches: Combining ExperianVerify with other security layers, like biometric authentication or behavioral analytics, to create a multifaceted shield against fraud.
- Regular System Audits: Periodic audits of verification workflows and data sources help identify vulnerabilities or gaps in security.
- Consumer Education and Transparency: Communicating verification procedures to consumers fosters trust and awareness, reducing fraudulent attempts predicated on misinformation.
Case Studies: Real-World Applications of ExperianVerify

Illustrative case studies demonstrate how organizations have harnessed ExperianVerify to enhance their credit security. For instance, a major online lending platform reported a 40% reduction in fraud-related chargebacks after integrating Experian’s advanced fraud detection tools. Similarly, a financial institution improved onboarding efficiency by reducing manual verification checks by 35%, thanks to tailored automation workflows enabled through ExperianVerify’s API integrations. These stories reveal tangible benefits, including fraud mitigation, customer experience improvements, and operational cost reductions. Such outcomes underscore the platform’s capacity to deliver strategic value when utilized correctly.
Challenges and Limitations in Using ExperianVerify
While the platform offers considerable advantages, certain challenges merit acknowledgment. For example, false positives—where legitimate applicants are flagged—can lead to customer frustration and operational delays. Careful calibration of verification thresholds is necessary to balance security with usability. Likewise, integration complexity can pose hurdles, particularly for legacy systems lacking compatible APIs. Moreover, data privacy concerns must be continually managed, especially in jurisdictions with stringent regulations. Staying ahead of fraud evolution demands continuous updates and potentially supplementary verification layers—an undertaking that requires committed resources and expertise.
Future Trends and Innovations in Credit Security Verification
The landscape of credit verification is dynamic, with emerging technologies promising even greater security. Facial recognition, biometric ID validation, and blockchain-based identity management are poised to complement existing systems like ExperianVerify. Additionally, the advent of artificial intelligence and machine learning enables predictive fraud detection, proactively identifying malicious behaviors before they manifest as breaches. Organizations leveraging these innovations—by integrating them with tools like ExperianVerify—may attain unprecedented levels of security resilience in the face of complex threats.
Summary: Strategic Utilization of ExperianVerify for Robust Credit Security
Utilizing ExperianVerify strategically equips organizations with a comprehensive, adaptive, and technically robust mechanism for safeguarding credit transactions and customer identities. From careful system integration and staff training to continuous monitoring and adaptation, the platform’s capabilities can significantly reduce fraud exposure. As threats become more sophisticated, so too must our tools and processes, with ExperianVerify standing out as a vital element of future-proof credit security strategies.
How does ExperianVerify improve overall credit security?
+ExperianVerify enhances credit security by authenticating identities in real-time, detecting suspicious patterns with machine learning, and ensuring compliance with privacy laws. Its comprehensive features minimize fraud risks during application processes and account management.
What are the best practices for integrating ExperianVerify into existing systems?
+Best practices include API customization suited to your workflows, establishing clear verification protocols, training staff thoroughly, and continuously monitoring verification metrics for calibration. Ensuring seamless system integration is key to maximizing security benefits.
What challenges might organizations face when deploying ExperianVerify?
+Challenges include managing false positives that could hinder customer experience, navigating integration complexities with legacy systems, and ensuring ongoing compliance with evolving privacy regulations. Regular system audits and calibration can mitigate these issues.
How could future technological developments influence ExperianVerify’s effectiveness?
+Emerging technologies such as biometric verification, blockchain identity management, and AI-driven predictive analysis will likely enhance ExperianVerify’s capabilities, making fraud detection more proactive and secure in an increasingly complex threat landscape.
